Architecture
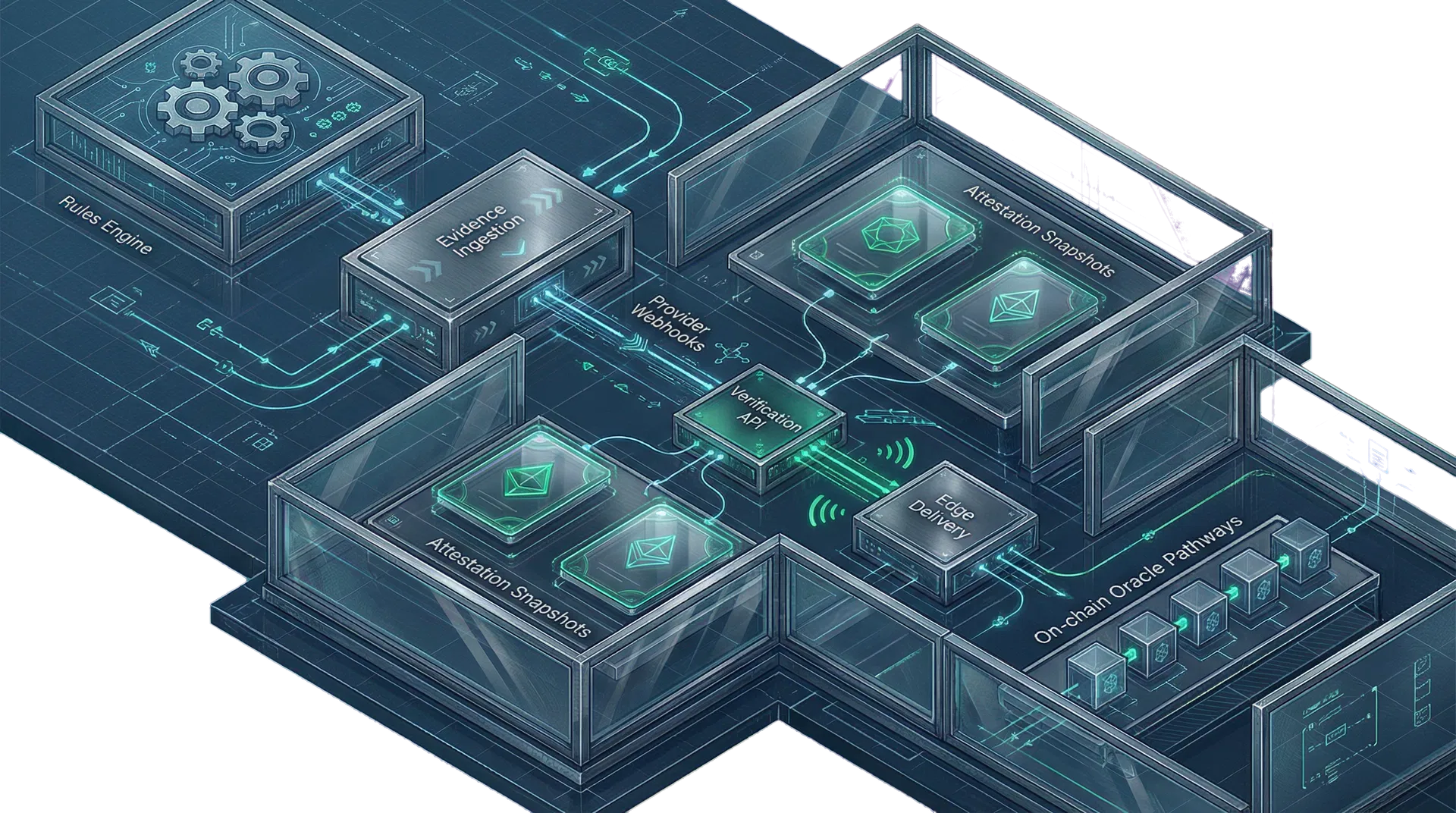
A blockchain compliance architecture that separates evidence, evaluation, and verification deliberately.
This page turns the architecture summary into a dedicated destination for technical buyers. It explains how OMINEX can keep evidence durable, attestation computation structured, and customer verification reads fast enough for real production traffic.
System overview
A verification path designed for fast reads and defensible auditability.
Rule configuration
Template-driven rule definitions can organize offerings, jurisdictions, provider requirements, and verification thresholds across blockchain compliance programs.
Evidence ingestion
API push, provider webhooks, suitability capture, bulk upload, and future chain-aware observations can feed a neutral attestation model without collapsing customer systems into one monolith.
Attestation snapshots
Derived, query-optimized records can reduce runtime recomputation and make verification retrieval fast, stable, and externally consumable.
Verification surfaces
Branded portals, signed payloads, partner APIs, and future on-chain delivery paths can expose auditable compliance state without leaking tenant boundaries.
Observed evidence, not approvals
OMINEX is designed to attest to observed fact. It can evaluate evidence against configured rules and publish verifiable status without becoming the compliance decision-maker itself.
Tenant-aware from the foundation
The architecture is shaped for multi-tenant delivery with organization boundaries, branded verification experiences, and controlled access from the database layer upward.
High-volume verification by design
The product direction centers on precomputed snapshots, signed envelopes, indexed read paths, and aggressive cacheability so customer systems can query at institutional scale.
A durable control plane
Authentication, relational data, storage, and trusted backend execution can support a structured control plane while still leaving room for specialized read paths as traffic patterns mature.
How reads stay fast
Verification traffic should resolve against prepared data, not against the full rules graph every time.
The highest-volume customer path should favor prepared attestation snapshots and stable envelopes. That allows verification APIs, branded portals, and partner systems to retrieve answers quickly while the richer evidence graph remains available underneath for auditability and recomputation.
How integrations stay manageable
Provider events, queue execution, and verification delivery can evolve independently.
A separated architecture gives OMINEX room to add provider-specific normalization, queue controls, signature hardening, and downstream SDK patterns without rewriting the core public verification contract every time a new source system is added.
Review endpoint structureNext step
Move from product curiosity to operating-fit review.
Schedule a buyer review, ask a product question, or start a licensing conversation without digging through extra navigation layers.